A new cybersecurity report found ransomware-based data leaks increased by 50% in the education sector and 39% in the healthcare sector.
The eighth annual Global Threat Report, released by CrowdStrike, a cybersecurity technology company, contains data and observations on the evolving global cyber threat landscape. The report dives into the rising cost of ransomware demands and the uptick in ransomware-related data leaks, along with a breakdown of the sectors most impacted.
The report determined ransomware-based data leaks in the education sector increased from 52 attacks in 2020 to 105 in 2021. Attacks on the healthcare sector increased from 94 to 154.
Overall, CrowdStrike’s report observed an 82% increase in ransomware-related data leaks in 2021, with 2,686 attacks as of Dec. 31, 2021, compared to 1,474 in 2020. On average, 2021 saw over 50 targeted ransomware events per week. Furthermore, attackers demanded an average of $6.1 million per ransom in 2021 — up 36% from 2020.
“For security teams on the front lines and those of us in the business of stopping cyberattacks and breaches, 2021 provided no rest for the weary,” says the report. “In the face of massive disruption brought about by the COVID-driven social, economic and technological shifts of 2020, adversaries refined their tradecraft to become even more sophisticated and brazen. The result was a series of high-profile attacks that rocked many organizations and, on their own, represented watershed moments in cybersecurity.”
A breakdown of the 10 most-affected sectors can be seen in the chart below.
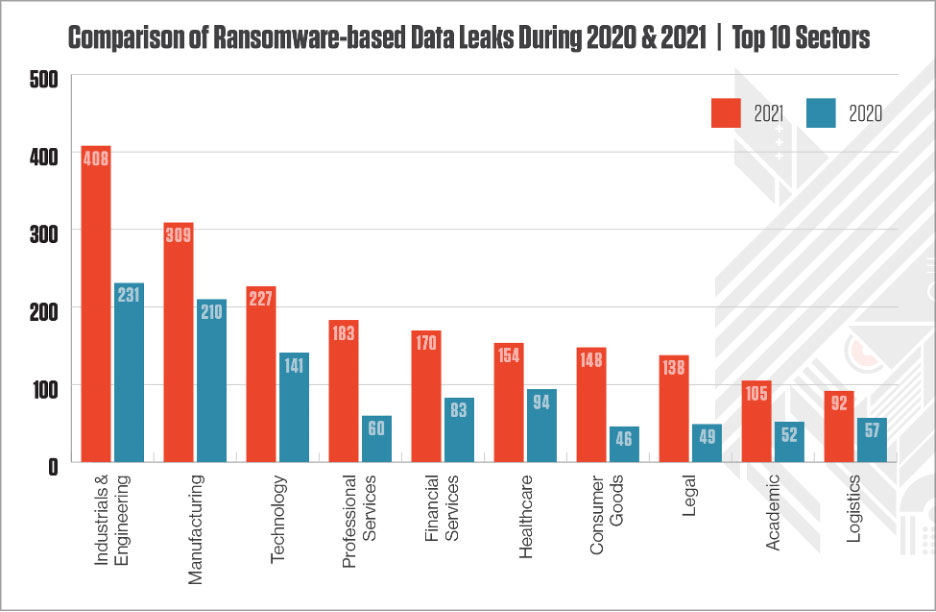
(Graphic: CrowdStrike’s Global Threat Report)
Other important findings from the study include:
- On average, eCrime adversaries need 1 hour 38 minutes to move laterally.
- 62% of attacks were malware-free, meaning they have moved beyond malware to use “hands-on-keyboard” techniques and “living off the land” tools to attempt to evade detection.
- There was a 45% increase in interactive intrusions and such attacks allowed adversaries to harvest new credentials and try to go undetected.
- Internet-facing devices were targeted with vulnerability exploits at elevated rates.
- Cloud environments face increasing threats since eCrime and targeted intrusion-focused adversaries are using remote code execution, credential theft, admin account abuse, command and control, and exploitation of misconfigured containers to advance their attacks.
Another co-authored report released by Crowdstrike in Nov. 2021 found 82% of hospitals had an IoT cyberattack between March 2020 and Sept. 2021. Of the hospitals that experienced an IoT attack, 34% were ransomware. The report also report found 33% paid the ransom and 31% of those hospitals did not get their data restored.
Most law enforcement agencies try to discourage compromised organizations from paying a ransom because it funds malicious groups. The FBI says organizations should not pay a ransom because it doesn’t guarantee that you’ll get data back and it encourages more ransomware activities.
However, a recent survey has found that 83% of ransomware victims give in to their attackers’ demands, and nearly two out of three organizations were victims in the past year.

