From it’s inception, the Health Information Technology for Economic and Clinical Health Act (or the HITECH Act) was intended to further enforce many rules within the Health Insurance Portability and Accountability Act (HIPAA). As such, understanding the HIPAA-HITECH relationship is an important task for healthcare officials.
The HITECH Act changed the standards HHS uses to evaluate hospitals, expanded the pool of organizations that must comply with those standards and bolstered the HHS Office for Civil Rights’ tools of enforcement.
Indeed, when HHS first announced HITECH, HIPAA enforcement policies were discussed extensively.
“The Department’s implementation of these HITECH Act enforcement provisions will strengthen the HIPAA protections and rights related to an individual’s health information,” then-OCR Director Georgina Verdugo said in a 2009 press release implementing the HITECH Act interim final rule. “Such heightened vigilance will give consumers greater confidence in the privacy and security of their health information and in the industry’s use of health information technology.”
The HITECH Act’s high-level purpose is “to promote the adoption and meaningful use of health information technology.” In that quest to push hospitals into the digital world, HITECH also made HIPAA more relevant and consequential to a much larger pool of people within the healthcare community.
Below we outline two of the most direct HIPAA-HITECH intersections to help readers wrap their heads around these complex laws (and avoid the costly penalties that can come with any confusion).

HITECH Broadens HIPAA Coverage
The HITECH Act made HIPAA relevant to a whole new class of organizations, with Subtitle D extending portions of HIPAA’s Privacy and Security Provisions to a broader class of “business associates.”
Previously, HIPAA defined a business associate as “a person who performs functions or activities on behalf of, or certain services for, a covered entity that involve the use or disclosure of protected health information.”
HITECH changed HIPAA’s definition of business associates to include:
- Health information organizations
- Patient Safety Organizations (PSOs)
- E-prescribing gateways
- People who offer personal health records to others on behalf of a covered entity
- People who provide data transmission services involving PHI to a covered entity AND require routine access to PHI
- “Subcontractors” that create, receive, maintain or transmit PHI on behalf of a business associate (thus subcontractors are anyone a business associate has delegated a function, activity or service to where that activity involves PHI)
HITECH did not revoke HIPAA exceptions to the business associate standard (outlined in HIPAA Sections 164.308(b)(2) and 164.502(e)(1)(ii)).
HITECH Categorizes HIPAA Violations, Tiers HIPAA Fines
Before the HITECH Act was enacted in 2009, the HHS’ Secretary was unable to impose penalties of more than $100 for each HIPAA violation or $25,000 for all HIPAA violations of the same type.
Prior to HITECH, HIPAA also allowed a covered entity to avoid a penalty if it could demonstrate that it didn’t know it was failing to comply with HIPAA.
HITECH Section 1176(a) created categories of HIPAA penalties meant to distinguish between the nature and extent of different violations and the harm they cause patients.
There are now three broad categories of HIPAA violations that correspond with different civil penalties. We have included a visual summary of these fines from the 2009 HITECH Interim Final Rule below:
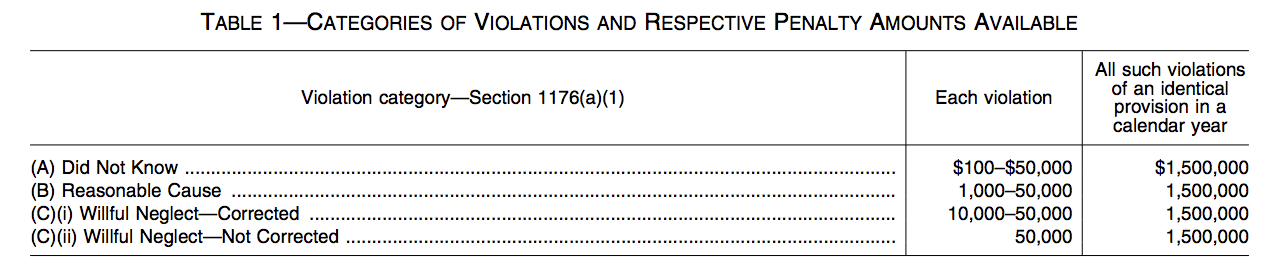
These fines are outlined in more detail below:
- If a HIPAA violation occurs in which the entity didn’t know and by exercising reasonable diligence couldn’t have known that a person violated a HIPAA provision, it will pay at least $100 for each such violation (and not exceeding $25,000 per calendar year), but not more than $50,000 for each violation (and not exceeding $1.5 million per calendar year).
- In the case of a HIPAA violation that’s due to reasonable cause (and not willful neglect), the entity will pay at least $1,000 for each violation but not more than $100,000 per calendar year. Reasonable cause is defined as “an act or omission in which a covered entity or business associate knew, or by exercising reasonable diligence would have known, that the act or omission violated an administrative simplification provision, but in which the covered entity or business associate did not act with willful neglect.’’
- In the case of violations due to willful neglect, there are two tiers of penalties. If the violation is corrected, the penalty is at least $10,000 for each HIPAA violation (and cannot exceed $100,000 per calendar year), but not more than $50,000 per HIPAA violation (and not more than $1.5 million per calendar year). If the violation is not corrected, then the penalty is at least $50,000 for each HIPAA violation (and not more than $1.5 million per calendar year). The HITECH Act stipulates further that “In determining the amount of a penalty under this section for a violation, the Secretary shall base such determination on the nature and extent of the violation and the nature and extent of the harm resulting from such violation.”

Examining The HIPAA-HITECH Connection Further
There are of course many other ways the HIPAA-HITECH worlds overlap. Both HIPAA and HITECH are such sweeping laws that they often address similar areas, particularly around electronic medical records, their “meaningful use” and PHI.
Thus as the HITECH Act further incentivized the healthcare community to use electronic health records, HIPAA’s privacy and security standards became more important, and cybersecurity threats to healthcare organizations like phishing attacks, ransomware and other hacks increased in relevance.
But the revised monetary penalty system seems to be the point of most concern for healthcare officials and their business associates responsible for securing health information technology (health IT).
Other provisions in the HITECH Act were more focused on patients, including:
- Incentivizing the “meaningful use” of electronic medical records by healthcare entities to improve patient care
- Requiring practices to notify patients of any unsecured data breaches. Learn more about HIPAA breach notification requirements here.
- Expanding patient’s right to receive electronic copies of their health information
- Modifying HIPAA’s individual authorization requirement to facilitate research and disclosures of child immunizations to schools and to enable access to decadent information by family members
- And much more!
HIPAA and HITECH are too complex to detail in full here. That’s why Campus Safety has been writing about the HIPAA-HITCH relationship for years.
Officials in the healthcare space need all the help they can get to understand these regulations completely. Campus Safety is happy to serve as a resource!
Editor’s note: Information in Campus Safety is intended to help readers understand complex regulatory landscapes but should not be interpreted as official guidance. Refer to the text of the actual laws for direct government instruction.

