Members of the healthcare industry are generally aware of the HIPAA breach notification requirements. Those HIPAA requirements include (if the breach affects the PHI of more than 500 individuals) notifying the individuals affected by the breach, the media and the HHS.
But healthcare entities must also provide a list of very specific information, and hospitals don’t want to slip up during a relatively simple HIPAA-compliance process.
And just in case hospital officials didn’t think the HHS’ OCR was willing to enforce the breach notification rule, the office enforced it for the first time earlier this year when it reached a $475,000 settlement with Presence Health.
The truth is breach notification should be conducted in a thorough, top-down manner that ensures HIPAA-covered entities meet each requirement completely.
To help covered entities check off each of these requirements, below we detail the three actions that must be taken under HIPAA following the discovery of a 500-plus person breach.
IMPORTANT NOTE: All of this must occur within 60 days of the breach discovery!
Notify Affected Individuals of The Breach (45 CFR Section § 164.400)
HIPAA-covered entities are required to inform affected individuals about a PHI breach by first class mail or email or, if contact information is out of date, entities can post a notice of the breach on its website’s homepage for 90 days or post the notice in “major print or broadcast media where the affected individuals likely reside.”
The notice, when possible, must include the following:
- A brief description of the breach (including the date of the breach and its discovery)
- A description of the type of information compromised in the breach (such as whether full name, social security number, date of birth, home address, account number, diagnosis, disability code, or other types of information were involved)
- The steps individuals should take to protect themselves
- A brief description of actions taken by the hospital to investigate and mitigate the breach
- A description of hospital actions taken to prevent future breaches
- Hospital or entity contact information for individuals to ask questions or learn additional information (this should include a toll-free telephone number, an e-mail address, website, or postal address)
Being up front, clear and apologetic in your notification can foster a trusting relationship between the hospital and the individuals affected in a breach (it will also help make your institution appear dedicated to fixing the situation when the media and the HHS’ OCR get involved later on).
Notify the Media (45 CFR Section § 164.406)
When the breach affects more than 500 people in a single state or jurisdiction, hospitals and other HIPAA-covered entities are also required to notify prominent media outlets in that jurisdiction, typically through a press release. This notification must include all of the information included in individual notices.
Notify the HHS Secretary of The Breach (45 CFR Section § 164.408)
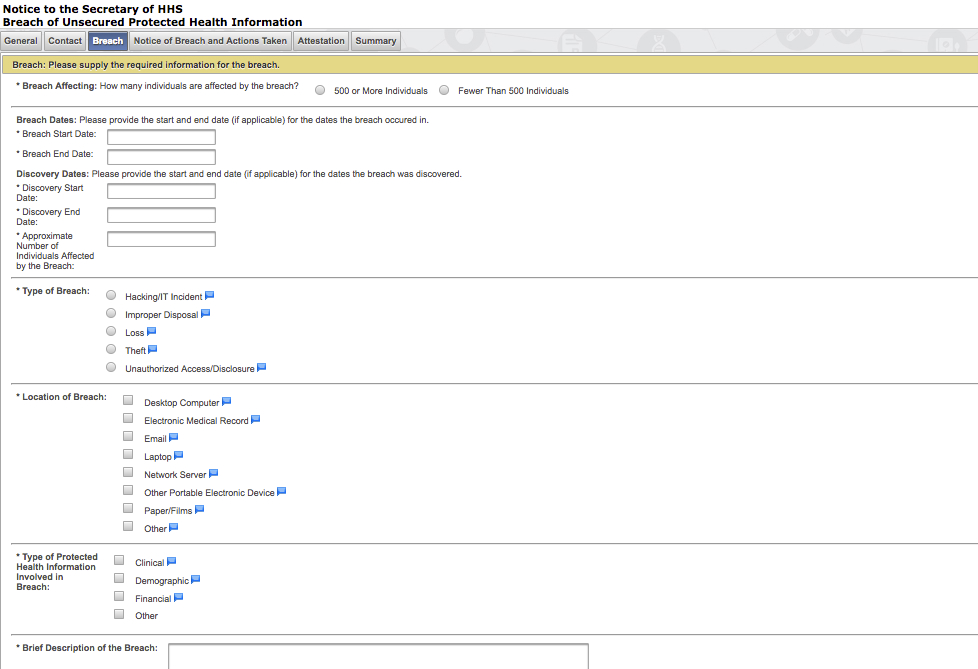
When submitting the breach to the HHS here, entities are asked to specify the following information:
- Breach dates
- Discovery of breach dates
- Type of breach
- Location of breach
- Type of PHI breached
- Give a brief description of the breach
- Check off safeguards in place prior to the breach
- Actions taken in response to the breach
A screenshot of the HHS breach reporting platform is included below:
After The HIPAA Breach Notification
If new information about the breach is discovered, hospitals must go back to the HHS’ web portal and submit an addendum to the initial report. Hospitals or other HIPAA-covered entities should also consider providing a 24/7 phone line and credit monitoring for the people affected.
Finally, at some point after the breach has been discovered, entities must change any passwords or authorizations that may have been compromised as part of its effort to mitigate the damage of the breach (remember, HIPAA requires breach mitigation to the extent it is practical (45 CFR 164.530(f)). As with all things HIPAA-related, be sure to document all of your efforts.
Sending PHI breach notifications is one of the easier parts of HIPAA compliance, but if officials aren’t careful when they’re sending notifications it just might trip them up!













